Nintendo 3DS
152 archivos
-
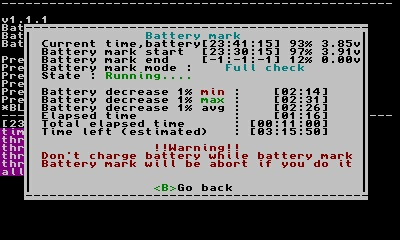
3DS Battery Checker
Check your 3DS battery.
by Core_2_Extreme.
-
3DS Homebrew Menu
3DS Homebrew Menu (new-hbmenu) es un simple y atractivo menú que muestra una lista las aplicaciones homebrew en formato .3DSX y nos permite ejecutarlas desde ahí mismo. Puede ser usado con los siguientes puntos de entrada:
Luma3DS Rosalina (recomendado): Funciona en todos los sistemas desde 4.0 en adelante. OFrece un acceso sin restricciones a los recursos del sistema de 3DS, además de ofrecer algunas características adicionales como depuración remote (GDB). hax 2.x, el sucesor de ninjhax. Sistema de carga de homebrew ya obsoleto que solo ofrece un acceso limitado a los recursos del sistema de Nintendo 3DS, y solo ataca a un nivel bajo de privilegios. El soporte para hax será eliminado próximamente. El homebrew de Nintendo 3DS es construido y distribuido en ejecutables con la extensión .3dsx. Puede que te encuentres algunos archivos con la extensión .cia. Estos no son ejecutables utilizando hbmenu.
Uso
Para instalar hbmenu, simplemente copia el archivo boot.3dsx al directorio raíz de tu tarjeta SD. Si estás usando una versión reciente de Luma3DS posiblemente ya tengas una copia de hbmenu isntalada, ya que viene incluído con esta aplicación.
Use the D-Pad, Circle Pad or the touchscreen to select an application, and press A or touch it again to start it. Use the C-Stick alternatively on New 3DS to scroll the list of applications.
On certain entrypoints (ninjhax 1.x and hax 2.x), it is not possible to go back to the 3DS HOME menu using the HOME button. As an alternative, you can press the START button where you can reboot your console or (in the case of hax 2.x) relaunch HOME menu.
hbmenu starts in the sdmc:/3ds/ directory for applications and it will look for 3dsx files inside it. You can navigate the directory tree and open/browse folders as you would expect. Old style application bundle folders are also detected, however this functionality may be removed in the future.
Here is an example directory structure that hbmenu will have no trouble recognizing:
sdmc:/ 3ds/ games/ Hermes.3dsx cubemadness.3dsx 3dscraft.3dsx blargSNES.3dsx gameyob.3dsx 3dnes.3dsx ftpd.3dsx Themely.3dsx If hbmenu does not find an icon file (either embedded in the executable or provided separately) to associate with a given 3dsx, it will display a default icon and the path to the executable as a fallback.
hbmenu also allows you to create "shortcuts" which are xml files containing a path to a 3dsx file and optional arguments to pass to the .3dsx. This file can also include a path to icon data as well as name, description and author text using tags as follows:
<shortcut> <executable>The path to the 3dsx file goes here.</executable> <icon>path to smdh icon data</icon> <arg>Place arguments to be passed to 3dsx here.</arg> <name>Name to display</name> <description>Description of homebrew app</description> <author>Name of the author</author> </shortcut> Arguments are space or tab separated but can use single or double quotes to contain whitespace.
Name, description and author will be read from the .3dsx if it has embedded SMDH data or from the supplied icon path. The fields in the xml file will then override their respective entries.
You should not hotswap the SD card while hbmenu is running since it compromises the 3DS OS's stability amongst other things. It is recommended that you instead use a file transfer homebrew application such as ftpd to transfer files without rebooting.
Technical notes
hbmenu does all its rendering in hardware thanks to the citro3d library. The 3DS system font is also used to render all text.
hbmenu uses some funky mechanisms to launch 3dsx files. If you're interested in launching 3dsx files from your own application, you should look here; although these mechanisms may change in the future.
Netloader
hbmenu contains support for the 3dslink protocol, which allows you to remotely load applications. Press Y to activate as usual then run 3dslink <3dsxfile> if your network can cope with UDP broadcast messages. If 3dslink says 3DS not found then you can use -a <ip address> to tell it where to send the file.
All the other arguments you give 3dslink will be passed as arguments to the launched 3dsx file. You can also specify argv[0] with -0 <argument> which is useful for setting the current working directory if you already have data files in a particular place, i.e. 3dslink myfile.3dsx -0 sdmc:/3ds/mydata/
3dslink is provided with devkitARM.
Credits
smea: code & original hbmenu version fincs: code & rewrite GEMISIS: code mtheall: code WinterMute: netloader code Fluto: graphics Arkhandar: graphics dotjasp: graphics (regionfree icon) gruetzkopf, TuxSH, AuroraWright, Soph1a7, SentientTurtle, Yami-chan, d3m3vilurr, daedreth, JixunMoe, yy-codes, MCPE-PC: translations -
3DS Multi EmuNAND Creator
Este programa está diseñado para inyectar / extraer volcados NAND hacia / desde el área de almacenamiento reservada en la tarjeta SD mediante herramientas como Gateway's Launcher.dat y EmuNAND9. Está completamente escrito en C y se puede compilar usando MinGW o TDM-GCC, sin la necesidad de bibliotecas adicionales y / o componentes de tiempo de ejecución.
Características
Detección automática de tarjetas SD que contienen una o más NAND (s). Puede inyectar / extraer hasta cuatro (4) NAND diferentes desde / hacia cualquier tarjeta SD dada (siempre que la capacidad de almacenamiento lo permita). Compatible con viejos volcados 3DS / 2DS y New 3DS / 2DS NAND. Admite formatos EmuNAND y RedNAND (desplazamiento de sector +1). Compatible con todos los diseños NAND existentes: 'Legacy' (utilizado por Gateway's Launcher.dat), 'Default' (tamaño NAND redondeado de 4 MB) y 'Mínimo' (tamaño NAND mínimo redondeado de 4 MB posible). Capaz de realizar la acción "Formatear EmuNAND", que permite particionar, formatear e inyectar un volcado NAND a una nueva tarjeta SD sin usar una consola Nintendo 3DS. Posibilidad de eliminar una NAND existente de la tarjeta SD reparticionándola y formateándola, ganando más espacio para la partición FAT en proceso. Si se elimina una NAND que precede a una o más NAND adicionales, también se perderán. La eliminación de NAND # 1 es equivalente a formatear la tarjeta SD sin una EmuNAND, p. Ej. recuperarás todo el espacio consumido por la (s) NAND (s). Posibilidad de establecer un nombre personalizado para una NAND, que CakesFW puede mostrar en su menú de selección Multi NAND. Agradecimientos a
Pete Batard, por desarrollar Rufus. Este programa usa código de Rufus en su procedimiento de formato FAT32. Todos mis amigos, que me ayudaron y motivaron para seguir adelante. La gente de GBAtemp, por probar cada nueva versión. Aplicación creada por DarkMatterCore.
-
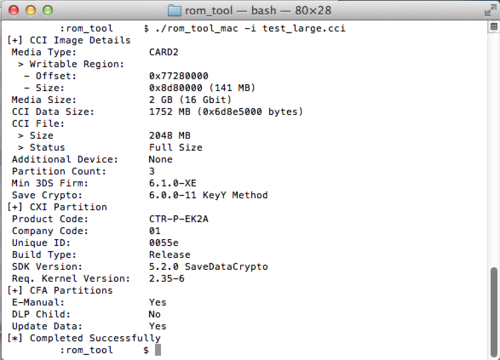
3DS ROM Tool
'rom_tool' is a command line tool designed to check/manipulate CTR Cartridge Image (CCI) files, usually referred to in the 3DS Scene as "3DS ROM dumps".
Its major use is to reduce the size of CCI files (trimming) by removing dummy bytes(and being able to restore them again). Trimmed CCI files are compatible with the Gateway 3DS flash cart, and associated clones.
-
3DS ROP xPloit Injector
Un instalador de unSAFE_MODE y menuhax67 basado en ROP, útil para los exploits de userland que no pueden lanzar el lanzador homebrew.
Esta herramienta está basada en ninjhax.
3DS ROP xPLoit Injector es una herramienta creada por PabloMK7.
-
3DS Ropkit
This is a codebase intended to be used with userland title exploits in general for Nintendo 3DS.
The exploit would use the scripts here for locating the required ROP addrs. Then in the .s, it would include "ropkit_ropinclude.s", and if this is an regular-application "ropkit_boototherapp.s".
Currently this is only usable with GCC with the "-x assembler-with-cpp" build option.
This requires ropgadget_patternfinder.
ropkit_boototherapp.s
This handles booting the otherapp *hax payload, various defines are required.
This automatically handles locating each 0x1000-byte page in .text used with the payload in physmem, across the entire APPLICATION memregion. Hence, this bypasses the codebin physmem randomization added with v10.4, which was later enabled for more titles with v11.0.
by yellows8.
-
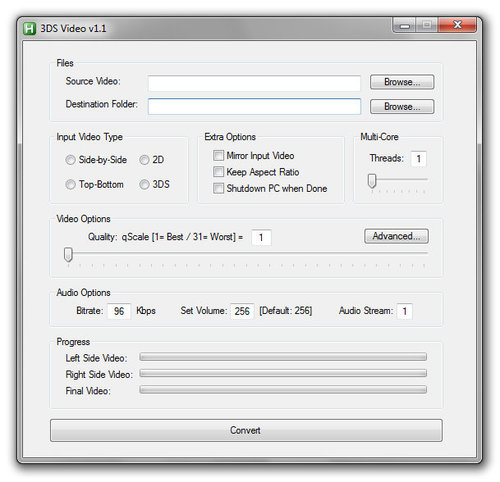
3DS Video
This is a program for converting videos to the 3DS.
Options:
Source Video - Choose the video you want to convert Video Folder - Folder to place converted video in (e.g. 3DS video folder) Format - Type of 3D video, or 2D video Quality - Quality (31 is lowest, 1 is max) Advanced... - Show advanced options (replace Quality with Bitrate & FPS) Bitrate - Bitrate of converted video Framerate - Framerate of converted video Notes:
The included ffmpeg.exe is 32-bit. If you have a 64-bit CPU, you may want to replace it.
Changelog:
-=v1.32=-
*Fixed: Simple Mode now rounds down the original framerate to the nearest integer and uses a maximum of 30 fps by BelowZero
-=v1.31=-
*Fixed problem with Progressbars when the program was canceled before
*Fixed MsgBox prompt in Simple Mode
-=v1.3=-
*Simple Mode now takes over the original framerate to a max of 30 fps by BelowZero
*Conversion of very short Testfiles works correctly now by BelowZero
-=v1.21=-
*Added choice of the duration of the test file option by BelowZero
-=v1.2=-
*Added media infos by BelowZero
*Added test file option by BelowZero
*Added several audio options by BelowZero
*Enabled upscaling of video framerate by BelowZero
-=v1.1=-
*Added keep aspect ratio option by amzg
*Improved progress bars by BelowZero
-=v1.00=-
*GUI rewrite by amzg
*Mirrored input option fixed by amzg
*Progress bars added by BelowZero and amzg
*New error if destination folder has spaces
*GUI is disabled while converting
-=v0.30=-
*Added mirrored input option
*Added option for 480x240 resolution (default is still 400x240)
-=v0.23=-
*More bug fixes (thanks to amzg, xxNathanxx and Guy.brush at GBATemp)
*Remembers video folder
*Source tidied a bit
-=v0.22=-
*Fix splitting 3D video (thanks to Stylpe at GBATemp)
-=v0.21=-
*Fixing (some of) the bugs of v0.2
-=v0.2=-
*Added auto-splitting of files
*Added "Advanced..." options
-=v0.15=-
*Fixed bugs of v0.1
-=v0.1=-
*Initial release
by SifJar.
-
3ds_browserhax_common
This repo is for intended for any 3DS title which has some form of web browser. This repo is for generating ROP-chains for use with the previously mentioned targets: no browser exploit(s) are contained in this repo. Browser exploits seperate from this repo can use this for the actual ROP-chain + any required ROP gadgets etc.
Supported titles and versions
The versions below are listed in the following format: browserver titlever sysver. Which browserver(target title + version of the title) to use is automatically determined by checking the user-agent. Due to this, when accessing hax with this, the New3DS system web-browser must be set to use the normal user-agent, not the mobile user-agent(the mobile user-agent is the same for all versions).
Also note that with the system web-browser, only the last number in the system-version(X.X.X-NUPVER) actually matters for the browser version. Loading arm11code with the Old3DS browser is only supported with >=v5.0 NATIVE_FIRM, if you want to use pre-v5.0 NATIVE_FIRM with this you would have to modify the source. Normally doing so isn't needed since the *hax payloads don't support system-versions that old anyway.
Only the USA, EUR, and JPN browsers are supported(with the exception listed below): the main ExeFS codebin are all identical for these regions, unlike the other regions.
Note that for CHN and TWN the loader(with 3ds_arm11code_chntwn.s) is broken(the menustub fails to auto-locate APT_GetServHandle due to older homemenu/ctrsdk code).
Old3DS system Internet Browser(spider):
1.7412 v6 2.0.0-2..2.1.0-3 1.7455 v1024 2.1.0-4..3.0.0-6 1.7498 v2050 4.0.0-7..4.5.0-10 1.7538 v0 4.2.0-9..4.5.0-10 This is the first version of the CHN+KOR (and probably TWN) browser. This is supported for CHN and KOR. 1.7552 v3075 5.0.0-11 / v3088/7.0.0-13 (v3088 main ncch is the same as v3075, only the manual CFA was updated) (that is, 5.0.0-11..7.0.0-13) 1.7567 v4096 7.1.0-16..9.5.0-22 1.7585 v5121 9.5.0-23..9.8.0-25 1.7610 v6149 9.9.0-26..10.1.0-27 CHN, KOR, and TWN are also supported for this. 1.7616 v7168 10.2.0-28..10.5.0-30 CHN, KOR, and TWN are also supported for this. 1.7622 v8192 10.6.0-31 CHN, KOR, and TWN are also supported for this. 1.7625 v9232 10.7.0-32..11.0.0-33 CHN, KOR, and TWN are also supported for this. Handled the same way as 1.7622. 1.7630 v10240 11.1.0-34 New3DS system Internet Browser(SKATER):
1.0.9934 v10 9.0.0-20..9.2.0-20 1.1.9996 v1027 9.3.0-21..9.5.0-23 1.2.10085 v2051 9.6.0-24..9.8.0-25 1.3.10126 v3077 9.9.0-26..10.1.0-27 KOR is also supported for this. 1.4.10138 v4096 10.2.0-28..10.3.0-28 KOR is also supported for this. 1.5.10143 v5121 10.4.0-29..10.5.0-30 KOR is also supported for this. 1.6.10147 v6144 10.6.0-31 KOR is "supported" for this but it's not tested. 1.7.10150 v7184 10.7.0-32..11.0.0-33 KOR is also supported for this. 1.8.10156 v8192 11.1.0-34 Exploit testing
If you want to test a browser exploit on an unsupported browser version just to see if it at least crashes, you can use this: "URL?browserver={ver}". Where ver is one of the browservers listed in 3dsbrowserhax_common.php, such as "85" for New3DS or "7" for Old3DS(without quotes), or whatever versions the exploit page supports.
Usage with seperate exploits
With php, this repo can be used with the following:
Include config based on browserhax_cfg_example.php, see that file for details. Include 3dsbrowserhax_common.php. Set the global $ROPHEAP variable to an address under the process which the ROP-chain can use for storing arbitrary data(for example, this could be memory where data was sprayed for non-ROP-chain data, since that data isn't needed anymore at this point). Call generate_ropchain(). This generates a ROP-chain which can be included in JS via the $ROPCHAIN global variable. To generate a binary-only ROP-chain instead, set the $generatebinrop global variable to value 1 before calling generate_ropchain(). The ROP-chain data can now be used for generating the final html/js, for example: "var ropchain = unescape($ROPCHAIN);" This can be used before the above ROP-chain data, for use as a ROP NOP-sled: "unescape($NOPSLEDROP);" This can be used for spraying the stack-pivot gadget address, like for vtable funcptrs: "unescape($STACKPIVOT);" This can be used when the exploit requires using the "pop {pc}" gadget: "$somestr.= genu32_unicode($POPPC);" Configuration
See above regarding the cfg file.
By default, when $ropchainselect wasn't initialized by browserhaxcfg_handle_urlparams(), it will set $ropchainselect to value0 and $arm11code_loadfromsd to value2. When this is with a spider version prior to system-version v7.1, $ropchainselect will be set to value1. Next, regardless of browser-version, it then calls browserhaxcfg_handledefault().
Values for $ropchainselect:
0: This "ROP-chain" is just an address for THROW_FATALERR. Hence, throw_fatalerr() will be triggered when the above browserhaxcfg_handledefault() path is executed when browserhaxcfg_handledefault() doesn't initialize $ropchainselect. 1: <=v4.x arm9hax also implemented by oot3dhax under EXECHAX=3, see 3dsbrowserhax_common.php generateropchain_type1(). 2: ARM11-code loading via gspwn, see $arm11code_loadfromsd below. The payload should be position-independent-code without any GOT, since the payload is loaded to R-X memory where the address varies per title version. The payload is called with r0 set to an address of a structure mainly containing funcptrs for various functions in the process, see generateropchain_type2(). r1 is initialized too for a relocated stack address if the payload needs it. The max payload filesize is 0x8000-bytes. At the start of this ROP-chain, the sub-screen colorfill is set to display yellow, at the end it's set to display gray. 3: Read the contents of a file then dump it to SD. This uses OPENFILEDIRECTLY. 3dsbrowserhax_common.php must be modified in order to use this, see generateropchain_type3(). At the start of this ROP-chain, the sub-screen colorfill is set to display red, at the end it's set to display blue. 4: This uses the service-access-control bypass fixed with system-version v7.0, then it uses NSS:RebootSystem. This can be used for region-free on system-versions below v7.0. This was originally implemented a while after the regionfree method with NSS:RebootSystem was originally discovered: http://3dbrew.org/wiki/3DS_System_Flaws#Standalone_Sysmodules Values for $arm11code_loadfromsd:
0: The arm11code payload is embedded in the ROP-chain data itself. 1: The arm11code payload is loaded from SD via this filepath: "sdmc:/arm11code.bin". 2: The arm11code payload is downloaded by requesting a binary with http, see the above example config and ropgen_httpdownload_binary() in 3dsbrowserhax_common.php. The binary is downloaded to SD, once it's finished with that the file has all-zeros written to it, then it attempts to delete the file(which doesn't actually delete the file, unknown why). Browserhax usage info
How each exploit is triggered depends on the exploit, see the documentation for the seperate exploit for that. As said below, just triggering the exploit successfully is all that's really needed besides SD "/boot.3dsx".
3DS Webkit exploits can be quite unstable. When a webkit exploit is very unstable, formatting the browser savedata is recommended if you haven't done so before with the current exploit URL. If you want, from hblauncher-payload booted via browserhax you could install exploit(s) listed here: http://3dbrew.org/wiki/Homebrew_Exploits
You can have the browser auto-load the exploit page if you return to Home Menu from that page. For exploits which automatically trigger, you may have to disable wifi/etc before attempting to load the page in order to return to Home Menu successfully before the exploit actually triggers.
Homebrew Launcher
This codebase is mainly intended for loading an arbitrary arm11code payload, at a vaddr which varies per title/version. Homebrew-launcher can be booted via this arm11code payload, with the loader included with this repo. The spider version of this loader automatically locates the required addresses and such on-the-fly. The New3DS web-browser is supported by this too, without anything that's system-version/region specific(besides the data loaded from the payload). The loader determines whether it's running under spider or SKATER by checking the New3DS flag loaded via NS(command 0x01020000 http://3dbrew.org/wiki/NS_and_APT_Services). Therefore, do not use this payload on Old3DS outside of spider, and on New3DS do not use this loader outside of SKATER.
In some cases on Old3DS, a crash/"hang" may occur with an orange or white bottom-screen. If it ever returns to Home Menu when the bottom-screen was orange, then a reboot is required.
This loader will initially try to load the hblauncher ropbin payload from SD-card "/browserhax_hblauncher_ropbin_payload.bin". This is separate from the otherapp payload.
If loading from SD fails, this loader will then automatically detect the required payload, then download it with HTTP. This latter method is highly recommended(unless this method doesn't work well for the user): with a "/boot.3dsx" on SD card, there's zero other setup/user-input needed once the browserhax is triggered successfully.
When loading the payload with both of the above methods fails, a crash will be triggered.
Hanging/crashing at an gray-bottom-screen means *hax payload loading failed, normally this is due to network issues(you should reboot your system when this happens).
The loader for Old3DS runs actual native code under the context of Home Menu, if you really want to run your own code under Home Menu you can modify that code in the loader. This code runs very early in the Home Menu process boot.
Screen colors
When using browserhax the bottom-screen colorfill will be set to various colors in the following order:
Yellow: Browser ROP started running, this also means the exploit itself worked fine. Gray: This colorfill is set right before jumping to the initial arm11code binary, for running native code for the first time. Orange: This is set after the *hax payload was successfully loaded into memory via HTTP/SD. White: This is set by the *hax payload itself when it starts running. Credits
megazig for helping with APT(for APT stuff once the Home Menu code in the loader starts running) during the initial + eventually successful Old3DS Home Menu takeover implementation.
-
3DSBank
Have you hit the 300 title limit on your 3DS, and/or want more than 300 titles, but don't want to make an EmuNAND (or 2nd one), or use another SD card?
The answer, is 3DSBank!
With this, you can store your Nintendo 3DS folder into a bank, and select or create another one to use, containing your other titles (and themes, and badges).
Adding custom names
The custom names can be defined in 3DSBank/3DSBank.ini like so:
[3DSBANK] SLOT_NAME_0 = Favorites SLOT_NAME_1 = More Fav. SLOT_NAME_2 = Homebrew Games etc.... Credits
DrStraightface: Updated source to allow custom naming of folders, and having currently active folder selected on startup.
by RocketRobz.
-
3DSController
A 3DS homebrew application which allows you to use your 3DS as a wireless controller for Windows.
Setup and Usage
Firstly, if you want to be able to register the circle pad or touch screen as a joystick you will need to install vJoy. However, if you just want to use keyboard buttons, this is not necessary.
Extract the archive and copy the executable in the 3DS directory with the extension that applies to your loader: 3DSController.3dsx and 3DSController.smdh for Ninjhax, 3DSController.3ds for flashcards, or 3DSController.cia for CFWs, into your 3DS's SD card or flashcard's micro SD card.
Copy the file 3DS/3DSController.ini to the root of your 3DS's SD card, and change the line that says IP: 192.168.0.4 to match your computer's local IP.
If you are unsure of your local IP address, run 3DSController.exe and it will tell you.
Run 3DSController.exe on your computer. If you are prompted, make sure to allow it through your firewall.
Start the application on your 3DS, there is no GUI, it will automatically try to connect to the IP address you put in 3DSController.ini.
If it wasn't able to read the IP from 3DSController.ini, it will notify you and quit.
Otherwise, you should just see a black screen, this is a good sign. To see if it works, open Notepad and press some buttons on the 3DS, they should show up. You can also test if the joystick works by going to Configure USB Game Controllers in Control Panel, it shows up as vJoy.
If using version 0.4 or above you can press L, R and X to bring up the keyboard. Press L, R and X again to close it.
If using version 0.6 or above, up to 16 joystick buttons are available. If you wish to use more than 8, you need to configure vJoy. Search in your start menu for vJoyConfig and set buttons to 16.
If using Ninjhax press Start and Select to return to the Homebrew Loader, otherwise you can just exit with the Home button.
Setup and Usage (Linux)
-For keyboard emulation Follow the Windows instructions, but use 3DSController.py instead of the EXE.
-For Joystick emulation, first, install python-uinput. BEWARE: The latest release of this library as of the writing of this tutorial is 0.10.2 which is broken for most updated systems. Download the master branch directly.
Make sure that uinput module is running. You can do it from cosole like so: #!sudo modprobe uinput
Then, follow the Windows instructions, but use 3DSController_gamepad.py instead of the EXE.
May work on OS X too, but this is not tested.
Configuration
Find the line Port: 8889 and change it to your desired port, do this for both the 3DS's 3DSController.ini and the PC's 3DSController.ini.
To use custom key bindings, just change the PC's 3DSController.ini file, it should be straight forward.
Configuration (Linux)
The configuration for the keyboard emulation is in 3DSController.py, not the INI.
The configuration for the joystick emulation is in 3DSController_gamepad.py, not the INI.
Troubleshooting
Make sure that you are using the 3DS and PC application from the same release, Make sure your 3DS has internet access (turn on the switch on the side of the 3DS so that an orange light shows) and is on the same network as your PC, Make sure that the 3DSController.ini is in the root of your 3DS's SD card (not flashcard micro SD), Make sure that the 3DSController.ini has the local IP of your computer, not your public IP, Make sure your firewall isn't blocking the application, Try using a different port (change the port for both the 3DS and PC's .ini file), by CTurt.
-
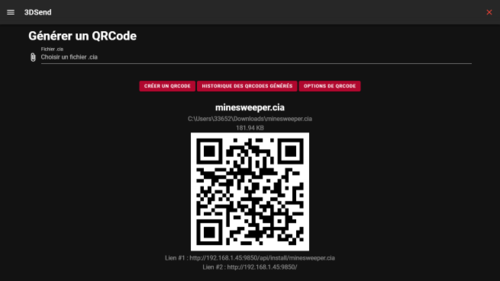
3DSend
Graphical interface under Windows and Linux allowing to install cias easily! : D
What is 3DSend?
3DSend is a Windows and Linux multi-platform utility allowing to install cias stored on a PC directly on a 3DS via FBI or any other application which can install cias thanks to a link or a QR code.
The main features of the application are:
The installation of CIAs from a PC on the same local network. An integration of TinyDB. A history to allow you to choose QR codes from the old ones generated. A choice of server port for people with a particular network configuration. The strong points of 3DSend:
Better performance compared to competitors (optimized application loading). Also works without internet access, only a local network is necessary (except for TinyDB). Works under Windows and Linux. -
3DShell
3DShell (pronounced 3D-Shell) - is a multi-purpose file manager GUI for the Nintendo 3DS.
The program is currently in its early stages and lacks many features that are currently in development. More information will be given once the program matures.
This program's design elements are clearly inspired by CyanogenMod's built in file manager, and so I take no credit for that.
Current features:
Storage bar (at the very top, just beneath the current working directory). Precise battery percentage using mcu::hwc Creating new folders Renaming files/folders File/folder deletion Copy/Cut files and folders Multi-select items for delete/cut/copy (using Y button) FTP server (Press select or tap the ftp icon to toggle) Image preview (If the image is around 400 * 480 which is the size of both screens, the image will be split in half and displayed. Have a look at the screenshots below). Support for the following image formats. PNG, JPG, GIF[un-animated], TGA (untested ->) HDR, PIC, PNM, PSD) Zip file extraction. Searching for directories (allows you to quickly visit a directory by clicking the search icon on the top right (bottom screen).) File properties - lets you view info on current file/folder. Screenshots - Press (L + R) -> (/screenshots/Screenshot_YearMonthDay-Num.bmp) Fast scroll - Use analog stick File's time-stamp Browsing CTRNAND MP3, vorbis (ogg), flac and wav playback support. (All thanks to deltabeard/MaK11-12) Dir list Sorting (alphabetical - ascending, alphabetical - descending, size - largest to smallest, and size - smallest to largest) Online updater (nightly/releases) Credits:
deltabeard/MaK11-12 for sound support. mtheall for ftpd. Steveice10 for allowing me to use his screen.c C3D code as a template to build and make modifications on. preetisketch for the banner. FrozenFire for the boot logo. -
3DSident
3DSident es una sencilla aplicación para Nintendo 3DS que nos permite checkear el firmware actual y la versión del sistema operativo de la consola de una forma simple y cómoda, de forma similar a lo que hace PSPident con PSP.
Funciones:
Detección de la versión actual del kernel, FIRM y sistema. Visualización de la versión inicial del sistema. Detección de modelo con nombre de código e información de hardware (Retail/Devboard/Debugger/Unidad de captura). Muestra el tipo de pantalla (TN/IPS). Muestra la región. Muestra el idioma. Muestra la dirección MAC. Muestra la serie. Muestra SDMC y NAND CID. Muestra el nombre de usuario NNID, el ID principal, el ID persistente, el ID de base transferible, el país y la zona horaria. Muestra el ID del dispositivo. Muestra el ID del jabón. Estado de carga de la batería. Estado de conexión del adaptador de CA. Porcentaje de la batería (porcentaje real de la batería mediante mcu::HWC). Muestra el voltaje de la batería (estimado) y el formato desconocido. Muestra el firmware de la MCU. Detección de SD. Muestra la capacidad de almacenamiento total y libre de la SD. Muestra la capacidad de almacenamiento total y libre de CTR. Muestra la capacidad de almacenamiento total y libre de TWL. (Exclusivo GUI) Muestra la capacidad de almacenamiento total y libre de TWL photo. (GUI exclusivo) Muestra el número de títulos instalados en SD y NAND. Muestra el número de tickets instalados. (Exclusivo de GUI) Muestra el estado y el porcentaje del deslizador de volumen. Muestra el estado y porcentaje del deslizador 3D. Muestra la intensidad de la señal Wifi. Muestra la dirección IP. Muestra el brillo actual. Muestra el estado del brillo automático. (Exclusivo GUI) Muestra el modo de ahorro de energía. (Exclusivo GUI) Muestra el modo de salida de sonido. (Exclusivo GUI) Muestra si la consola es una unidad de depuración. (Exclusivo GUI) Muestra el estado de la toma de auriculares/audio. (Exclusivo GUI) Estado de la ranura de la tarjeta y tipo de tarjeta insertada (CTR/NAND). Muestra el pin de control parental, la dirección de correo electrónico y la respuesta secreta. (Exclusivo GUI) Muestra el ID del menú de inicio. Muestra información de la ranura Wifi (SSID, contraseña y dirección MAC). Muestra la semilla de código amigo local original/NAND. 3DSident es una aplicación creada por joel16.
-
3DStris
A Tetris clone for the Nintendo 3DS.
-
Acekard 2 Official Firmware
Official firmware for the Acekard.
How to use ak2
Please copy akmenu4.nds and folder __ak2 to the root of your TF card. And copy the rom or homebrews to any folders of your TF card. Then insert your TF card to your ak2 and insert your ak2 to DS. Turn on your DS and enjoy!
-
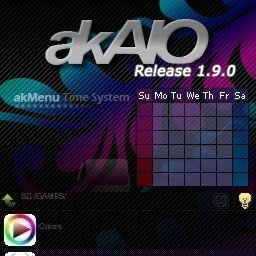
AceKard All-In-One (AKAIO)
AKBBS has been usurped thanks to amazing efforts of Normmatt in merging firmwares!
AK-AIO is custom system software for *BOTH* the AceKard RPG and AK2/AK2i.
Base features
-------------
For those unfamiliar with all the additions the AKBBS (now AIO) software has in comparison to the stock firmware, here's a sampling of the bigger changes:
* Cheat Improvements - R4/XML Cheat File processing
* "Future Adaptable" Multi-loader support
* Multiple Save Slots per title - with copying between slots
* Slot-2 Integration - EZ3in1 (w/GBA Patching) and older FlashAdvance Pro carts
* Shortcut tweaks
* Multi-page Start Menu
* Filetype-based external icon support
* Per-Rom settings for soft-reset/download play/cheats
* Copying/Cutting/Deleting SAV files along with NDS files
* Several improvements to 2byte language support
* SAV backup/restore from within GUI (.SAV<->.BAK)
* Wifi updating of Loaders
Version History
---------------
AK-AIO 1.9.0
+ More of a "Game Fix/Compatibility" release
+ Pokemons, Pokemons, Pokemons compatibility fixed
+ Updated to compile with latest DevKitArm
+ Cheats updated to CMP Cheat code Database version 6/29/2012
AK-AIO 1.8.9z
+ All this time for just a "z" in file version? Yes.
+ Finally fixed per-file/extension custom icons... broken since 1.8.0
+ Update loader to Mighty Morphin Power Loader release (Jan 2012)
+ Not much else; poor DS seems to be lonely with its 2D-ness :(
AK-AIO 1.8.9
+ Internal name listing mode will show the filename if there's a lack of info (e.g. - DS Program File)
+ Arm7 fix for slow windows in 1.8.8
+ Many, many, many game fixes
+ New default skin (EvoI)
+ Optimizations in icon display
+ Code cleanup to reduce memory usage
AK-AIO 1.8.8a
+ Fixed display problems with some bmp files.
AK-AIO 1.8.8
+ Updated to devkitARM r34 and libnds 1.5.2
+ Added two small icon view modes: Filename and Internal Name
+ Touchscreen scrolling has been inverted by default
- Mimics touchscreen phone/tablet scrolling
- Can be toggled in Advanced Settings screen
+ FAS1 Modifications to allow modifying specific SRAM Banks and dumping the entire 256KB SRAM
- Options in the FAS1 Menu
+ Added support for 24bit and 32bit bitmaps for skins
- Note these get down sampled to 16bit so no increase in available colors.
AK-AIO 1.8.7
+ Added Wifi Cloud Save button to Akmenu.
+ Added Russian translation (Thanks mc_B3oWoL).
+ Added Danish translation (Thanks oz8hp).
+ Updated Korean translation (Thanks cherries4u).
+ Updated Spanish translation (Thanks felixsr).
+ Updated Dutch translation (Thanks Jodyza).
AK-AIO 1.8.6a
+ Fixed real cart being detected as clone after softreset.
AK-AIO 1.8.6
+ Fixed left spin box sometimes having text on it.
+ Fixed spin box width calculation.
+ Cheat Window now uses 60% less memory for scrolling cheats/notes. Finally!
AK-AIO 1.8.5
+ Fixed usrcheat parsing bug where enabled codes in folder caused a crash during parsing.
+ Fixed PassMe booting for Slot 2 (L+A on Slot 2 icon).
+ Fixed bricking on old AK2s.
AK-AIO 1.8.2
+ New Anti-Anti-Piracy work around (enabled by default).
- Works on all SD and doesn't break download play.
+ Fixed various ak2 only bugs. (global settings being reset after softreset, etc)
AK-AIO 1.8.1
+ Updated French translation (Thanks corenting).
+ Updated German translation (Thanks SignZ).
+ Updated Korean translation (Thanks cherries4u).
+ Fix GBA Auto saving.
+ Fix some corruption issues.
+ Optimize .cc parsing.
AK-AIO 1.8.0
+ New Filesystem library (should be more reliable and less buggy than libfat).
+ Adjusted key repeat delay from 3 seconds to 1 second.
+ zLib updates since lord knows how long it's been since that was first added
- Credit to GPF for sources (http://gpf.dcemu.co.uk/)
+ Added ability to delete non-empty folders.
+ Changed the way the list is sorted so its case insensitive.
+ Fix custom icons.
+ Updated French translation (Thanks corenting).
+ Updated German translation (Thanks WiZaRd).
+ USRCHEAT.DAT is now maintained by yusuo and hosted at akaio.net
- TempDB in Wifi Plugin replaced by AKAIO (yusuo)
- WhatsNew works for it as well
- We have complete control of your cheats. Be afraid.
+ Added Anti-Anti-Piracy work around.
- This seems to break single card download play atleast for now so its disabled by default.
- On AKRPG it creates a filename.ap file for each game you launch with the option enabled.
- On AK2 it creates an ap.bin file in the __aio folder.
+ Fixed usrcheat.dat parsing when the game is the last in the file.
AK-AIO 1.7.1
+ Updated English language file.
+ Added option to disable Icon Animations.
+ AKRPG SD now works the same way as AK2/AK2i.
- Direct SD Saving.
- Save size set to 512KB unless a bigger size is needed.
+ Added some shortcuts:
- L+UP = Cheats enabled for selected game.
- L+DOWN = Cheats disabled for selected game.
- L+LEFT = Soft-Reset enabled for selected game.
- L+RIGHT = Soft-Reset disabled for selected game.
+ Added Cheat Scrolling speed option
+ Fixed Wifi Settings Window not saving what you've chosen
+ Wifi easter egg?
AK-AIO 1.7
+ Updated Brazilian Portuguese translation (Thanks Cereal Killer).
+ Updated Polish translation (Thanks Tatsuhikki).
+ Updated Czech translation (Thanks penthaler).
+ Added Norwegian translation (Thanks Glisern).
+ Updated Italian translation (Thanks Miottolo).
+ Updated Korean translation (Thanks cherries4u).
+ Added Thai translation (Thanks kikukiku).
+ Add option to disable homebrew softreset globally.
+ Add homebrew softreset support for libnds 1.4.3 (IRQ hooking only)
+ Updated savelist.bin
+ Added Yellow Wood Goblin's updated GBA ROM patching routines.
+ Fix GBA rom as shortcut detected as NDS rom bug.
AK-AIO 1.6 RC2
+ Show error screen on boot if your using a clone.
+ Added Korean language (Thanks cherries4u).
+ Added Czech language (Thanks penthaler).
+ Fixed hiddenFileNames ini bug.
+ Now shows an error if a clone is detected.
+ Updated savelist.bin
AK-AIO 1.6 RC1
+ Fixed Internal Name language setting.
+ Fixed Time Stamps on save files.
+ Fixed Setting Skin and Language at the same time not saving.
+ Homebrew Softreset (AK2/AK2i Only).
+ AK+ loader removed (Unsupported since it was first added in 1.0).
+ Fixed some cheat window bugs.
+ Fixed custom icon bug.
+ Updated homebrew argv support.
+ Updated savelist.bin
AK-AIO 1.5.1
+ Fix Date/Time retrieved from files.
+ Fix Cheat Window Freeze/White screen problem. (Thanks Baka_Kyuubi84 for the test case)
+ Added Swedish language file. (Thanks the_engineeer)
+ Added Brazilian Portuguese language file. (Thanks Cereal Killer)
+ Updated savelist.bin
+ Zelda now defaults to the required 1MB (If your using a 512kb save you will need to start again because the save file is corrupt, Alternatively you can manually set the save size backto 4Mbit and continue but it will cause problems later into the game).
+ Fix disk icon appearing over other windows.
+ Settings window shows long filenames for skins and languages now.
AK-AIO 1.5
+ Fixed issue with the hiddenFileNames globalsettings option not accepting non lowercase filenames.
+ Optimizations to the AK2 dldi should be a little quicker now.
+ Update Dutch translation (Thanks MarioWaza).
+ Update Spanish translation (Thanks Pendor).
+ AK2/AK2i clones are now officially unsupported.
+ Gba icon has been removed from main selection screen on DSi.
+ Removed outdated plugin system.
+ Per rom GBA frame support (256x192x15bpp)
- Place BMP with internal game id of gba rom in __aio/frames.
+ Added support for save sizes up to 256Mbit (32Megabyte).
+ .sav is now default save extension.
+ Reverse Alphabetical List sorting (set sortListAlpha=0 in globalsettings.ini).
+ Auto-Anti-Piracy Patcher updated.
+ ARGV support for homebrew.
+ New DSi detection (Shouldn't show slot2 icon after softreset on ak2i now).
+ Disable start menu by adding "LockStartMenu = 1" to your globalsettings.ini
+ Fixed Trainer Toolkit support.
Please refer to LoaderChangelog.txt for compatibility fixes.
AK-AIO 1.4.1
NOTE: It's recommended you delete your optionlist.bin file in the __aio folder when updating to this release as the file structure has changed.
+ Soft reset Improvements.
+ Fixed corrupt Language files (Italian, German and Japanese).
+ Added missing font needed for chinese.
+ Added setting for Hide Extensions to the settings window.
+ Fix optionlist.bin corruption.
+ Spin boxes wrap around.
+ Game Fixes (DMA-Save Mode):
- Princess Maker 4
- Club House Games
- Mario and Luigi RPG 3
- Rune Factory A Fantasy Harvest Moon
- Animal Crossing (Currently cannot be run in this mode, force usage of DMA mode).
- Hidamari Sketch Dokodemo Sugoroku x 365
+ Game Fixes:
- Grand Theft Auto Chinatown Wars (U) Thanks gelu.
- Mario and Luigi RPG 3 (J) (new patch, thanks gelu).
- Layton 3 (J) (new patch, thanks gelu).
- Animal Crossing.
+ Updated French language (jp33).
+ Fix backlight always enabled on DS Phat.
+ Fix the Per-File icon problem if you have similar games (e.g. - Golden Sun.gba and Golden Sun 2.gba)
- In blissland, GOLDEN~1 is the same as GOLDEN~5
+ Wifi Updater has lots of fixes relating to GBATemp's new, crappy, server and its timeouts
- We appreciate the hosting, but seriously... everything needed to be rewritten to adapt to the crap speeds
NOTE: DMA-Save mode is now default so DMA mode (red loading text) is now enabled by holding X during loading.
AK-AIO 1.4
+ Settings window uses tabs now, merging Settings, Advanced Settings, and Patches options (Thanks Gelu)
- Use L/R to cycle through tabs
+ Misc cleanup of the gui.
+ 3in1 options now have FAS1 settings merged (detects 3in1/FA at selection, displays options accordingly)
+ Language files have some addition "title" additions/changes
+ Leapyear code fixed because the DS sucks at reporting variables nicely.
+ Updated German language (moviecut).
+ Reset more of arm7 before runing a game (Thanks Gelu).
+ 3in1+ Fix for Opera (Untested, Thanks cory1492).
+ Game fixes:
- 3369 Mario and Luigi RPG 3 (J) fixed.
AK-AIO 1.3.5 (Unreleased)
+ Game fixes:
- 0645/0777 Star Trek Tactical Assault
- General save fixes. (Thanks Gelu for noticing a silly bug).
+ New Patching Mode hold X while launching a rom.
- Fixes video and sound glitches which occur in old patching modes.
- NOTE: This is still experiental so it isn't default.
+ Folders now show their size in the Info window.
+ Soft Reset fixes.
AK-AIO 1.3.1 (Unreleased)
+ Game fixes:
- 1752/2314 My Spanish Coach fixed.
- 2243/2412 Pokemon Mystery Dungeon Explorers of Darkness fixed.
- 2385 Daigasso Band Brothers DX fixed.
- 2906/2971 Star Wars The Clone Wars Jedi Alliance fixed.
+ Unnecessary Guru Meditation screens on the AKRPG is fixed.
+ Soft Reset fixes.
+ Copying files should work better.
+ Game icons that rely on the nds firmware's background will display properly (Thanks Gelu).
+ Misc cleanup.
AK-AIO 1.3
+ AK2i support (options that could potentially harm AK2i are disabled)
+ Loaders are now external and can be updated separately to the GUI.
- Updated Wirelessly! (choose Loader Update in Wifi Update option of Start Menu)
- Small changelog, download, update all possible
- Loaders only updated for card being used (e.g. - AK2 users only download ak2loader)
- Resume supported
- Many loaders are beta, know this and shut up
- Manual download page @ http://akaio.gbatemp.net/loaders/
+ Wifi Cheat Update has resume support!
- Prompts after confirming you wish to "Try Again"
+ Files are now sorted alphabetically (Forced at the moment, sorry).
+ Added Some of Gelu's patches:
- Faster Directory Listing.
- New List mode - Internal nds names.
- Lots of Soft Reset Fixes for the AKRPG.
- new DMA mode and BBDX save fix for the AKRPG.
- font system (fully supports unicode now :D).
- New FIFO IPC System (Behind the scenes stuff).
- Massive amount of soft reset fixes mainly for the AKRPG.
- Game fixes (Brain Age 2 (K), Chrono Trigger (U/J),...).
- Added a few game related fixes (Think Kids, Tropix, Bleach 2).
NOTE: because of new font system, language files now need to be utf8. Some have been converted such as English and Japanese but others will need to be saved as utf8 to work properly.
+ Japanese games now show Japanese characters in rom info window when language isnt set to Japanese
+ Added a few game related fixes (Yoshi's Island, Star Trek, NSMB).
+ Files are now sorted alphabetically (Forced at the moment, sorry).
+ Pokemon Diamond/Pearl/Platinum can now read saves for R/S/E/FR/LG from ewin and 3in1 (AK2 Only for now).
+ Cheat engine fixes. (AK2 and AKRPG only for now).
+ Optimizations all round (Shouldn't have any lag in GUI anymore, also shouldn't experience any lag while saving).
+ Italian language added, language updates for English
+ New 3in1 options window.
+ Show GBA internal name in Internal view mode.
+ 3in1 internal GBA rom header stuff and work on Save/Load prompts in 3in1 options window.
- Enable/Disable saving 3in1 SRAM on startup (Enabled by default)
- Enable/Disable prompting before saving/loading SAV<->SRAM (recommended!)
- Enable/Disable the Universal Sleep Hack for GBA games
- Blank NOR button added for quick erase
- Dump SRAM button will manually dump the SRAM to a timestamped .sav file in the root
- 3in1+ support (untested, but routines and discovery are in, Opera and Rumble sources not available yet)
- Thanks to all donators!
+ Fixed some issues with the cheat window.
- Folders that only allow one cheat selected now function properly
- Separate icon for skinners for single-select folders (see included skins)
+ Animal Crossing cheats on AK2. (Use the v1.1 rom as v1.0 will not work anymore).
+ Unicode font loads on a per-ROM basis
- Default font is "kochi-mincho-subst.pcf" in /__aio/fonts directory, old unicode font removed (was 2x the size)
- Skinners may add their own custom font to their ui's directory
- New line in uisettings.ini "customUnicodeFont = xxxxxx.pcf" will load that font instead of default
+ Ability to hide extensions by manually adding "hideExtension = 1" to globalsettings.ini
+ DMA mode on AK2 (Hold A while loading a game to use non-DMA mode: Red text = DMA / Blue text = non-DMA).
+ New Super Mario Brothers Minigames on AK2: If they don't work, set Download Play to "Disabled" and boot in non-DMA mode (hold down A while loading)
+ Misc bug fixes (Too many to list).
AK-AIO 1.2
+ New AKRPG/AK2 Detection Routine which has proven to be much better
+ Cheat Update functions run from plugin, giving full memory access to it and allowing updates without full AKAIO updates
- Can choose to download USRCHEAT.DAT or CHEATS.XML and whether or not to display "Whats New" before launching
- Should be much more stable, perhaps a teeny bit faster
- Third option in "which cheat file to download" box displays the setting window at plugin launch, can be used for future expansion
+ Uses gelu's latest fixes for BBDX on the RPG (only works from MicroSD) - excellent work, gelu!
- Also has some other fixes gelu's put in for 3in1 NOR erasing, etc.
- gelu = the AKRPG master.
+ Preliminary AK+ Support. Very preliminary. As in, no help offered but know it's still being worked on (See: AK+ SUPPORT)
+ New Experimental Cheat engine for AK2 and AKRPG, please report any bugs
+ EZIV compatiblity fixed without need for special line in globalsettings.ini
+ Scrolling Non-unicode Cheats/Notes, toggle in Advanced Options (default: on)
- Can also call cheat window in ROM Properties with SELECT (if button is visible)
+ Simple Internal Text Reader
- System Settings -> TXT Viewer
- Parses text, add bookmarks with X, scroll between bookmarks with L/R Buttons
- Not as fast as native TXT plugin due to pre-processing of text files, perhaps if we had the TXT Plugin source things could be done, but that would make sense.
+ Per ROM rumble settings, ROM Options window
+ Listview mode remembered
+ 3in1 Support should be fixed, with thanks to cory1492 for testing
+ GBA Frame issue with Slot-2 booting from main list fixed
+ Asian languages should be better supported, since we're compiling the menu with DevKitARM 21
+ Variable Height Scrollbars and clickable arrows in cheat window/internal TXT viewer. 3 new BMPs for skinning: scrollbar_t.bmp/scrollbar_m.bmp/scrollbar_b.bmp
+ Super awesome hidden poweroff button in help window, add your own "poweroff.bmp" to "__aio" for fun
AK-AIO 1.1
+ USRCHEAT.DAT wifi updating support from within shell
- Connects to Narin's GBATemp site, displays WhatsNew.txt, downloads, unzips, replaces in one step
- UpdateDB option in Start Menu -> More -> UpdateDB
- zlib thanks to GPF (http://gpf.dcemu.co.uk/)
- Download speed limited by DS routine IPStack
+ (AK2) Alternate loader support, place loader(s) in "__aio/ak2loader/"
- ROM options window, select the AK2 loader to use to launch ROM
- Compatible with AceKard official loaders
+ (RPG) uses gelu's latest 4.09e13 softreset routines
- Updated 3in1 routines to all of gelu's latest
+ Fixed Dragon Quest 5 (AK2/AKRPG)
- Can now get off the ship and save file wont be rolled back
+ Can change save file extension (.nds.sav or .sav)
- Extension conversion: .SAV file Info Window, press "Save Ext." button
- Will convert all Save Slot SAV files as well
+ Scans for cheats on ROM Info Window (.DAT only), if exist "Cheat" button displays
+ Per file icon support (32x32x15bpp)
- place BMP with same name in same dir as file (eg: nesDS.bmp for nesDS.nds)
+ (Source) Variable spinbox width/General cheatlist cleanups/Scrolling Messageboxes
+ (Source) Minor changes to the cheat window
+ Fixed save size problems
- Shouldn't have any more problems with save sizes
+ Misc Skinning fixes
- Fixed problem with Adv.Evo skin
- Form titles moved up 1 pixel
+ SAV<->BAK routines now use native AK functions
AK-AIO 1.0
+ Runs on both AK2 and AKRPG
+ Uses gelu's latest AKRPG rom loader
+ Uses latest AK2 4.07a16 rom loader
+ Contains everything from AKBBS1.99
+ Future support for larger than 4mbit save types (only supports 64mbit at the moment)
+ Applied Bliss' AR Engine fixes to the AKRPG
+ Hopefully fixed most of the soft reset issues with the AKRPG
Special Notes
-------------
Seeing as this release has experimental support for saves ranging all then way up to 128mbit, please err on the side of caution and backup your saves before using this firmware.
The "__RPG" and "__AK2" directory is now simply called "__AIO"
Existing users should make sure to rename their system directory, and update globalsettings.ini to reflect the new hidden directory.
Known Bugs
----------
There are no known bugs
ToDo
----
* Fix any bugs that crop up
Also
----
Cheats included are from Rayder's awesome compilation at GBATemp, now maintained by Narin, and are current as of the date of this release.
For the most up-to-date files, check GBATemp's release site (http://cheats.gbatemp.net/), either via PC or by using the "UpdateDB" option in the start menu.
-
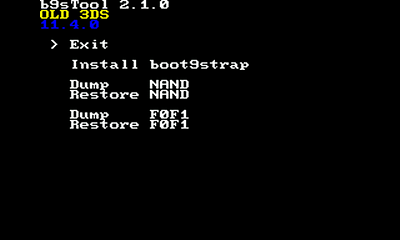
b9sTool
WARNING: Never, under any circumstance, use this homebrew in conjunction with a youtube/video guide of any kind! General Info
This app only writes to FIRM0, not FIRM1, so it should be safe given your FIRM1 is not corrupt or a9lh'd. Never use this on anything but 3DS FIRM 11.8.X-YZ. NEVER use this if arm9loaderhax or sighax is installed (on any firmware)! The result will be a brick! Compiling:
Just supply the current decrypted FIRMs for both new/old 3ds and put them in the firm_new and firm_old directories respectively. Then place the newest boot9strap.firm payload in the payload directory. Then compile with make FIRM_INFO="11.8 only" or whatever is actually the firmware range of the current native firm. The user does not have to supply any extra files like in previous versions. Needs the latest libfat version. Important b9sTool 5.X.X differences to 4.X.X
BACKUP.bin:
This has been removed. This feature was made in the interest of safety, but the realization that the update trick can reliably restore corrupted firms made it redundant.
It was also a pain in the ass.
xorpad_0123ABCD.bin
This is dumped to your boot9strap folder when b9s is installed. It isn't used now but may be useful in the future. Don't delete it.
The hex number in the filename is the first 4 bytes of the file's SHA1.
Cycling firm types:
When you install boot9strap multiple times, the standard behavior is that it will cycle between b9s and stock firm.
Don't count on this though, it's just a property of xoring operations and really isn't intended.
It is recommended you only install boot9strap once.
Firmware info:
4.0.1 - 5.0.0 is for firmware 11.8 ONLY (always check the firmware in the app menu to be sure as this can change as new firmwares are released!) 4.0.0 is for firmwares 11.4 to 11.7 ONLY Be careful using b9sTool between firmware updates - only use b9sTool on the firmware it's intended for. Credits
zoogie, plailect -
Bannerbomb3
This is a POC for a new System Settings userland exploit.
It uses ROP execution to dump DS Internet from System Settings using a custom crafted dsiware export.
This is useful primarily as an enhancement for "Fredminer" variant of seedminer to obtain free cfw on 3ds.
Among other things, it brings free cfw to more regions*, and removes the possibility of Nintendo pulling certain games like Steel Diver from the eshop to thwart homebrew efforts.
~~~ Hbmenu? ~~~
I've been able to get otherapp.bin booting by using 3ds_ropkit and a loader ROP chain. However, shortly after the bottom screen turns yellow, the 3ds just reboots to home menu.
It's really alright though. Fredminer gets you a more stable 3dsx homebrew environment anyway, so this isn't really a high priority issue right now (still would be cool to see hbmenu booting I admit).
~~~ Exploit ~~~
Basically put, this overflows the banner title strings in DSiWare exports (TADs) when you view them in System Settings, and smashes the stack leading to ROP control for the attacker.
You do need the movable.sed to encrypt a payload TAD, but that's easy enough to do nowadays. Movable.sed bruteforcing now only takes about a minute and free online services can do it for you. Over 350,000 people have done it so it can't be that hard :p
~~~ Q&A ~~~
Q: What's with the 3 in Bannerbomb3?
A: It's a tribute to the Wii scene, they did 1 & 2. I love old homebrew scenes.
Q: Why TADmuffin?
A: Muffin sounded funny so I went with that. Just needed to be different from TADpole.
Q: Will this work on the DSi since it has DSiWare exports too?
A: The flaw is definitely there as well, but I've been unsuccessful exploiting it on hardware (I can get code exe on no$gba though). Moot because of Memory Pit anyhow ;)
Q: Is this your first 3ds userland exploit?
A: Yes. Feels good man.
~~~ Thanks ~~~
- Yellows8 for 3ds ropkit
- All the people on #3dsdev, reading my backlog (Ctrl-F "pivot") provided a wealth of good info on the art of stack pivoting.
- Nintendo Homebrew Discord for maintaining online tools/guides and helping all the seed/frog/fredminer users. I hope this sploit makes your jobs a little easier.
- Jhynjhiruu for testing
by zoogie.
-
Batch CIA 3DS Decryptor
Batch CIA 3DS Decyptor es un simple archivo .bat que descifra archivos CIA y 3DS para principiantes. Los archivos .CIA se descifrarán y se convertirán en CCI o solo se descifrará la CIA para que se pueda instalar en Citra.
Uso de Batch CIA 3DS Decryptor
Coloca los juegos XXX.cia y XXX.3ds, DLC y parches en esta carpeta, admite múltiples archivos. Ejecuta "Batch CIA 3DS Decryptor.bat". Esperar a que el proceso se complete y listo. Nota: Se necesitará mucha memoria / RAM cuando estos archivos sean demasiado grandes).
Funciones y efectos:
Descifra archivos CIA y 3DS. DLC / Patch CIA> CIA descifrado, capaz de instalar en Citra. Juegos 3DS> 3DS descifrado y recortado, por lo que el archivo resultante ocupa menos. Juegos de la CIA> CCI descifrado (NCSD), no CXI (NCCH). Detección automática del tipo de CIA (DLC / Patch / Game). Autores:
54634564 - decrypt.exe profi200: makerom.exe, ctrtool.exe matif - Batch CIA 3DS Decryptor.bat -
beeShop
GUI for 3DS Network Installing.
How to use:
NOTE: Make sure your 3DS and the computer you're using beeShop on are on the same network if you're using the first or second install method. If they aren't, you won't be able to send the files/URLs over to your 3DS.
Download & extract the latest beeShop release (preferrably into a separate folder). Get ahold of a database file (.CSV) in format composed of Name,URL (either made by yourself or from other sources) and put it somewhere easily accessible. On your 3DS, open FBI > Remote Install > "Receive URL's over the Network" and note down the IP of your 3DS (don't close FBI after doing this). Launch beeShop, and click on the Settings button to open the Settings menu. You can configure lots of stuff in there, but right now, you need to press on the Select button on the top right hand corner. This will open a file selection dialog. Select a database (.CSV) file whose values should be in this format: Name,URL. Then, write the IP Address of your 3DS in the text box below IP:, select your preferred install method, and finally click on Save. beeShop should ask you to restart. Allow it. If your selected install method is Download & Install on 3DS:
Make sure your 3DS is in FBI > Remote Install > Receive URLs over the Network. Select an entry of your choice from the list and click on Install. If everything went right, beeShop should send the download link for the selected entry to FBI, which will ask you to install. Press A to do so. NOTE: beeShop will stay on Status: Installing while your 3DS is downloading in FBI.
If your selected install method is Download on PC, install on 3DS:
Make sure your 3DS is in FBI > Remote Install > Receive URLs over the Network. Select an entry of your choice from the list and click on Download. The selected entry will now be downloaded and a message box will show (entry) was successfully downloaded. once it's done. Now, click on the Install button and choose the file (.CIA) that was downloaded (it will be located in the same directory where beeShop.exe is located). This will send the file to FBI, which will ask you whether you want to install or not on your 3DS. Press A to install.
If your selected install method is custom-install: WARNING: custom-install is intended for advanced users only. Damage and or corruption may occur in some cases. Make sure you have a backup of your SD card just in case. You'll get shown this exact same warning when beeShop starts with custom-install as the selected install method.
Open the settings menu and click on the Configure custom-install button. This will open yet another window where you can specify the different files/paths needed for custom-install. Here's what you need: The SD card content encryption key from your 3DS (movable.sed) The ARM9 Bootrom of your 3DS (boot9.bin) How to dump various 3DS files A seed database for games that require seeds to function (seeddb.bin) (required, beeShop won't launch custom-install without this) Specify a valid drive letter in the first text box (D:/ for example). Select your movable.sed file in the second text box. Select your boot9.bin file in the third text box. Select the seeddb.bin in the fourth text box.
Click on save.
Get CIAs (app files). These must be sourced by yourself or by using the second install method. Make sure you have your SD card inserted into your computer. (and that you have the correct drive letter specified in the custom-install settings). On the main window, click on Install, which will open a file selection dialog. Select a .CIA file. If you have checked Show custom-install command line window, that window will open so you can see what's happening. Once it finished installing, you have to use custom-install-finalize on your 3DS to install a ticket for the installed title. Credits:
manuGMG & TimmSkiller DexterX12 Tools used:
Steveice10 - (servefiles.py and sendurls.py) ihaveamac - (custom-install) Translators:
TimmSkiller (German Translation) CiN CiN (Italian Translation) raccoon (French Translation) Eidwood (Catalan Translation) GrabsZel (Portuguese Translation) Testers:
Mineplanet84 MyPasswordIsWeak Mike Kaiju Kelonio Note:
beeShop does not encourage piracy and is only a way of gathering homebrew applications to a modded Nintendo 3DS System.
-
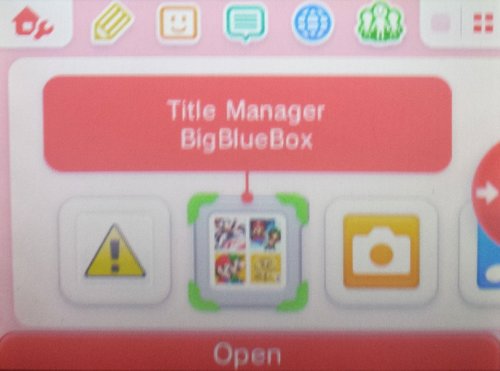
BigBlueMenu - BigBlueBox
Well heres a menu to manage all your CIA files
You can just use the .3DS file to run and install or install the .cia to your console so its always there mucher newer than the old DevMenu version everyones using
Enjoy as Always
-
Boot9strap
Boot9/Boot11 code execution.
Install via SafeB9SInstaller.
Launches "boot.firm" off of the SD card or CTRNAND. Hold Start + Select + X on boot to dump the bootroms/your OTP.
Credits:
Normmatt: Theorizing the NDMA overwite exploit.
TuxSH: Help implementing bootrom payloads.
Luma3DS: Codebase used in the stage 2 FIRM loader.
Licensing:
This software is licensed under the terms of the GPLv3.
You can find a copy of the license in the LICENSE file.
-
BootNTR
Allows you to use cheats ingame.
Install with FBI.
-
BootNTRSelector
A mod of BootNTR which will allows you to choose the version of NTR you want to load (and it is also much faster than regular BootNTR).
Installation
CIA
Install the .cia file through FBI and run it.
3DSX
Copy the .3dsx file into sdmc:/3ds/BootNTRSelector/ and run it through the New Homebrew Menu.
How to use
Launch BootNTRSelector through your method of choice and follow the on-screen instructions, no extra steps or files are required.
BootNTRSelector will now default to whichever NTR version you selected last.
Notes for Old3DS users
You need to use one of the Mode3 releases in order to use NTR with extended memory games (such as Monster Hunter, Pokémon Sun/Moon, Smash Bros, etc.). Mode3 has no effect on New3DS.
Launching BootNTRSelector before the home menu is completely loaded may result in a crash / error. So before launching it, wait a couple of seconds for the home menu to be fully loaded.
by Nanquitas.
-
CFW Suite
A collection of tools which can be used to modify some of the text from a DS or DS Lite firmware, to create a custom firmware (CFW).
Code from Chism, Loopy, Lick, and others has been used.
Steps to modify the "Touch the Touch Screen to continue." text
Dump original firmware
(Optional but recommended) install a version of FlashMe, this adds a failsafe to your firmware so you can recover if a future flash fails. Dump your DS firmware using DSBF Dumper. Modifying the firmware
Compile guiTool by running make, Extract gui data from your firmware with guiTool firmware.bin -e gui.bin, Make any changes you want to the gui.bin file (note: text is Unicode), the "Touch the Touch Screen to continue." text starts at 0x2c20 in the file. Make a copy of your firmware (here it is called cfw.bin), Inject gui data into your custom firmware with guiTool cfw.bin -i gui.bin, (Optional but recommended) run DeSmuME, go to Config->Emulation Settings and configure it to boot from your custom firmware; this is just to test that it works, Flashing to hardware (fwManager - recommended method)
Compile fwManager by running make, or download a prebuilt binary, copy it to your flashcard, Make a new directory called firmwares on your flashcard, Place your modified firmware (cfw.bin) here, Run fwManager and select your custom firmware; when the installer is running, short the SL1 terminal as if you were installing FlashMe. Flashing to hardware (FlashMeInjector - old method for homebrew loaders that don't support libfat)
Compile FlashMeInjector by running make, Inject your firmware into the FlashMe installer with FlashMeInjector flashme.nds -lite cfw.bin if you are using a DS Lite, or FlashMeInjector flashme.nds -phat cfw.bin if you are using an original DS, Run your modified FlashMe installer on your DS, FlashMe firmwares have an additional checksum, which will be incorrect, FlashMe will tell you the correct one and won't flash anything, Correct the FlashMe checksum with the one your DS told you, and inject the new firmware back into flashme.nds, Run flashme.nds again, from here the installation process will be the same as if you were installing FlashMe normally (SL1 must be shorted), If you follow the optional steps, then the risk of a brick will be relatively low; however, I take no responsibility if a brick does happen as a result of using these tools.
Uninstalling
Assuming you kept a backup of your original firmware, you can flash it with fwManager. Alternatively you may use noflashme.
No content owned by Nintendo is contained in this repo!
No firmwares are here, you must dump your own. The firmwares contained in the FlashMe installer have been removed, you must inject your own if you are using FlashMeInjector.
by CTurt.
-
Recientemente actualizado
-
Novedades populares






.thumb.png.9972ebc2dc30304f2f15faed6cdb73a2.png)